1086 字
5 分钟
cheetsheet
1. 代理
1.1. ssh
- socks5 走 ssh 隧道实现代理
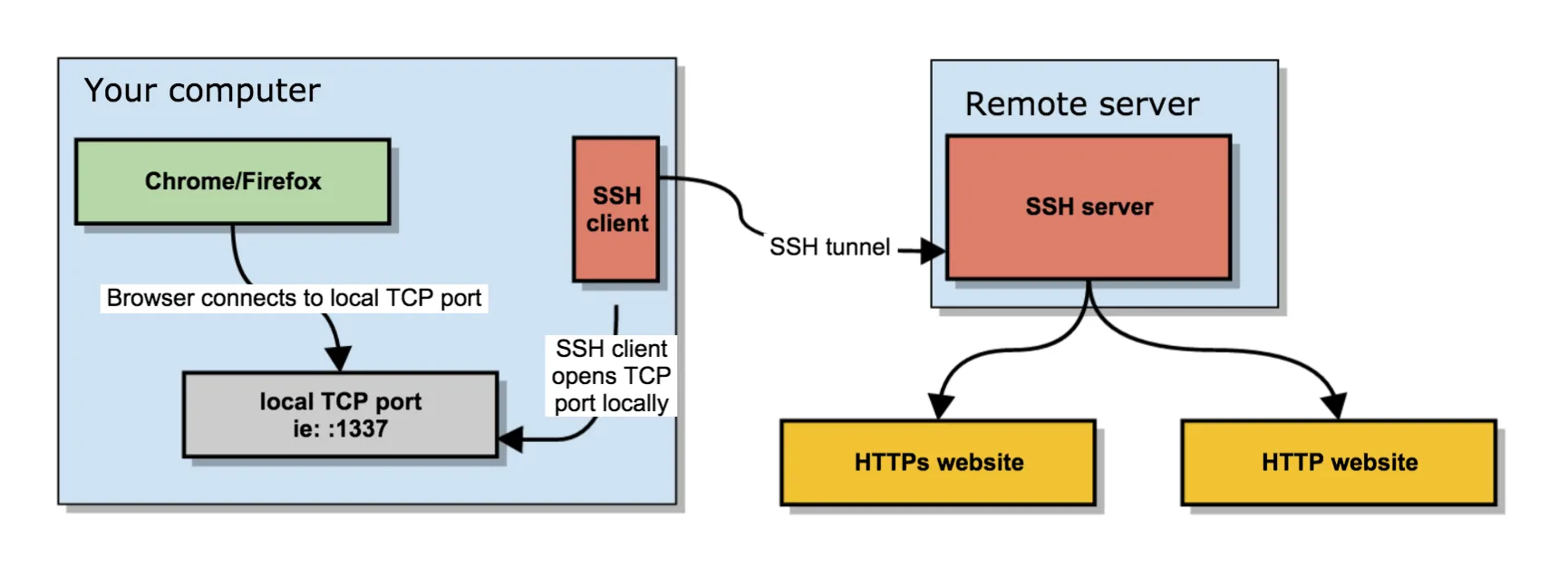
# -D:指定本地监听IP和端口
# -q:静默模式
# -C:压缩节约带宽
# -N:不执行远端命令,仅转发流量
# -f:在后台运行
# user@remote:远程用户@远程主机
ssh -D 0.0.0.0:1337 -q -C -N -f user@remote- 其他
# 本地端口转发 ssh -LNf local-port:target-host:target-port tunnel-host
# -L:转发本地端口。
# -N:不发送任何命令,只用来建立连接。没有这个参数,会在 SSH 服务器打开一个 Shell。
# -f:将 SSH 连接放到后台。没有这个参数,暂时不用 SSH 连接时,终端会失去响应。
ssh -L 3306:192.168.31.194:3306 root@127.0.0.1
# 远程端口转发 ssh -R target-port:local-host:local-port tunnel-host
# -R:转发远程端口。
ssh -R 9999:192.168.2.3:9999 root@1.1.1.1
# 通过~/.ssh/config配置github代理
#Host github.com
# HostName github.com
# ProxyCommand nc -v -X connect -x 127.0.0.1:9999 %h %p2. Android
2.1. adb
adb reboot bootloader # 进入fastboot
adb shell am start -a android.intent.action.VIEW -d scheme:// # 访问指定url
adb shell settings put global http_proxy 127.0.0.1:9999 # 设置代理
adb shell settings put global http_proxy :0 # 取消代理
setenforce 0 # 关闭SELinux
setprop persist.device_config.runtime_native.usap_pool_enabled false # 关闭usap
settings put system screen_off_timeout 100000000 # 设置屏幕常亮2.2. fastboot
fastboot reboot # 重启
fastboot boot boot.img # 临时进入boot镜像
fastboot flash boot boot.img # 刷入boot镜像2.3. 逆向
- Android Backup 包
java -jar abe.jar unpack cat.ab cat.tar # Android Backup包转换- jadx
jadx-gui --show-bad-codes # jadx无损启动- Xamarin 逆向
import sys, struct, lz4.block, os.path
def main():
if len(sys.argv) != 2:
sys.exit("[i] Usage: " + sys.argv[0] + " in_file.dll")
in_file = sys.argv[1]
with open(in_file, "rb") as compressed_file:
compressed_data = compressed_file.read()
header = compressed_data[:4]
if header != b'XALZ':
sys.exit("[!] Wrong header, aborting...!")
packed_payload_len = compressed_data[8:12]
unpacked_payload_len = struct.unpack('<I', packed_payload_len)[0]
compressed_payload = compressed_data[12:]
decompressed_payload = lz4.block.decompress(compressed_payload, uncompressed_size=unpacked_payload_len)
out_file = in_file.rsplit(".",1)[0] + "_out.dll"
if os.path.isfile(out_file):
sys.exit("[!] Output file [" + out_file + "] already exists, aborting...!")
with open(out_file, "wb") as decompressed_file:
decompressed_file.write(decompressed_payload)
print( "[i] Success!")
print( "[i] File [" + out_file + "] was created as result!")
if __name__ == "__main__":
main()2.4. 系统证书
# 计算证书pem格式的hash
openssl x509 -subject_old_hash -in a.pem
# 重命名<hash>.0
mv a.pem <hash>.0
# Create a separate temp directory, to hold the current certificates
# Without this, when we add the mount we can't read the current certs anymore.
mkdir -m 700 /data/local/tmp/htk-ca-copy
# Copy out the existing certificates
cp /system/etc/security/cacerts/* /data/local/tmp/htk-ca-copy/
# Create the in-memory mount on top of the system certs folder
mount -t tmpfs tmpfs /system/etc/security/cacerts
# Copy the existing certs back into the tmpfs mount, so we keep trusting them
mv /data/local/tmp/htk-ca-copy/* /system/etc/security/cacerts/
# Copy our new cert in, so we trust that too
cp /data/local/tmp/<hash>.0 /system/etc/security/cacerts/
# Update the perms & selinux context labels, so everything is as readable as before
chown root:root /system/etc/security/cacerts/*
chmod 644 /system/etc/security/cacerts/*
chcon u:object_r:system_file:s0 /system/etc/security/cacerts/*
# Delete the temp cert directory & this script itself
rm -r /data/local/tmp/htk-ca-copy3. Frida
3.1. 堆栈打印
Java.perform(function () {
var SQLiteDatabase = Java.use("com.tencent.wcdb.database.SQLiteDatabase");
SQLiteDatabase["open"].implementation = function (
bArr,
sQLiteCipherSpec,
i15
) {
console.log(
Java.use("android.util.Log").getStackTraceString(
Java.use("java.lang.Throwable").$new()
)
); //java层打印堆栈
console.log(
"open is called" +
", " +
"bArr: " +
JSON.stringify(bArr) +
", " +
"sQLiteCipherSpec: " +
sQLiteCipherSpec +
", " +
"i15: " +
i15
);
var ret = this.open(bArr, sQLiteCipherSpec, i15);
console.log("open ret value is " + ret);
return ret;
};
});3.2 函数 hook
Java.perform(function () {
var e = Java.use("ir3.e");
e["r"].implementation = function (str, str2, i15, z15) {
console.log(
"r is called" +
", " +
"str: " +
str +
", " +
"str2: " +
str2 +
", " +
"i15: " +
i15 +
", " +
"z15: " +
z15
);
var ret = this.r(str, str2, i15, z15);
console.log("r ret value is " + ret);
return ret;
};
});4. Windows
4.1. hyper-v
Enable-WindowsOptionalFeature -Online -FeatureName Microsoft-Hyper-V -All # 开启hyper-v5. 证书
5.1. openssl
ssh-keygen -y -f ~/.ssh/id_rsa # ssh-keygen导出公钥
openssl x509 -in a.cer -inform der -out a.pem -outform pem # der to pem6. Docker
6.1. Docker Desktop version on Mac
# https://stackoverflow.com/questions/64221861/an-error-failed-to-solve-with-frontend-dockerfile-v0
export DOCKER_BUILDKIT=0
export COMPOSE_DOCKER_CLI_BUILD=0
# snap docker 国内源
# /var/snap/docker/current/config/daemon.json
# {
# "log-level": "error",
# "registry-mirrors": [
# "https://docker.mirrors.ustc.edu.cn"
# ]
# }7. Linux
7.1. 扩容
# lvextend -L 10G /dev/mapper/ubuntu--vg-ubuntu--lv //增大或减小至19G
# lvextend -L +10G /dev/mapper/ubuntu--vg-ubuntu--lv //增加10G
# lvreduce -L -10G /dev/mapper/ubuntu--vg-ubuntu--lv //减小10G
# lvresize -l +100%FREE /dev/mapper/ubuntu--vg-ubuntu--lv //按百分比扩
sudo lvresize -l +100%FREE /dev/mapper/ubuntu--vg-ubuntu--lv
# 执行resize2fs使扩容生效
sudo resize2fs /dev/mapper/ubuntu--vg-ubuntu--lv7.2. 自动挂载
crontab -e
# @reboot mount /dev/sdb /home/docker/data7.3. 命令行操作
for i in *; do mv $i ${i}.zip; done # 批量加后缀
for i in *; do mv $i ${i%.*}.zip; done # 批量改后缀
SCRIPT_DIR=$( dirname $(readlink -f $0) ) # 当前目录8. Mysql
# 创建账号及修改账号权限
CREATE DATABASE bizsec CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci;
CREATE USER 'bizsec'@'%' IDENTIFIED BY 'password';
GRANT ALL PRIVILEGES ON bizsec.* TO 'bizsec'@'%';
FLUSH PRIVILEGES;
SELECT User, Password, Host FROM mysql.user;9. NodeJS
npm config set registry http://mirrors.cloud.tencent.com/npm/ # 配置
npm config get registry # 验证9.1. elecetron 反编译
# https://stackoverflow.com/questions/38523617/how-to-unpack-an-asar-file
npm install -g @electron/asar
npx @electron/asar extract app.asar app # Extract the whole archive:
npx @electron/asar extract-file app.asar main.js #Extract a particular file: